Introduction
Dependabot is a GitHub tool that analyses your project dependencies, and keeps you informed about any issues on security, outdated versions etc., and also helps in automating the package update by raising a pull request against your code repo. This is a very very useful tool as it would be impossible manually to know what issues are coming up with new updates on each and every package around the world. So ensure you onboard to this tool, and make the best of GitHub, and also Dependabot!
This article describes how Dependabot works and how it upgrades and fixes Node.js dependencies or in general NPM packages used in your projects.
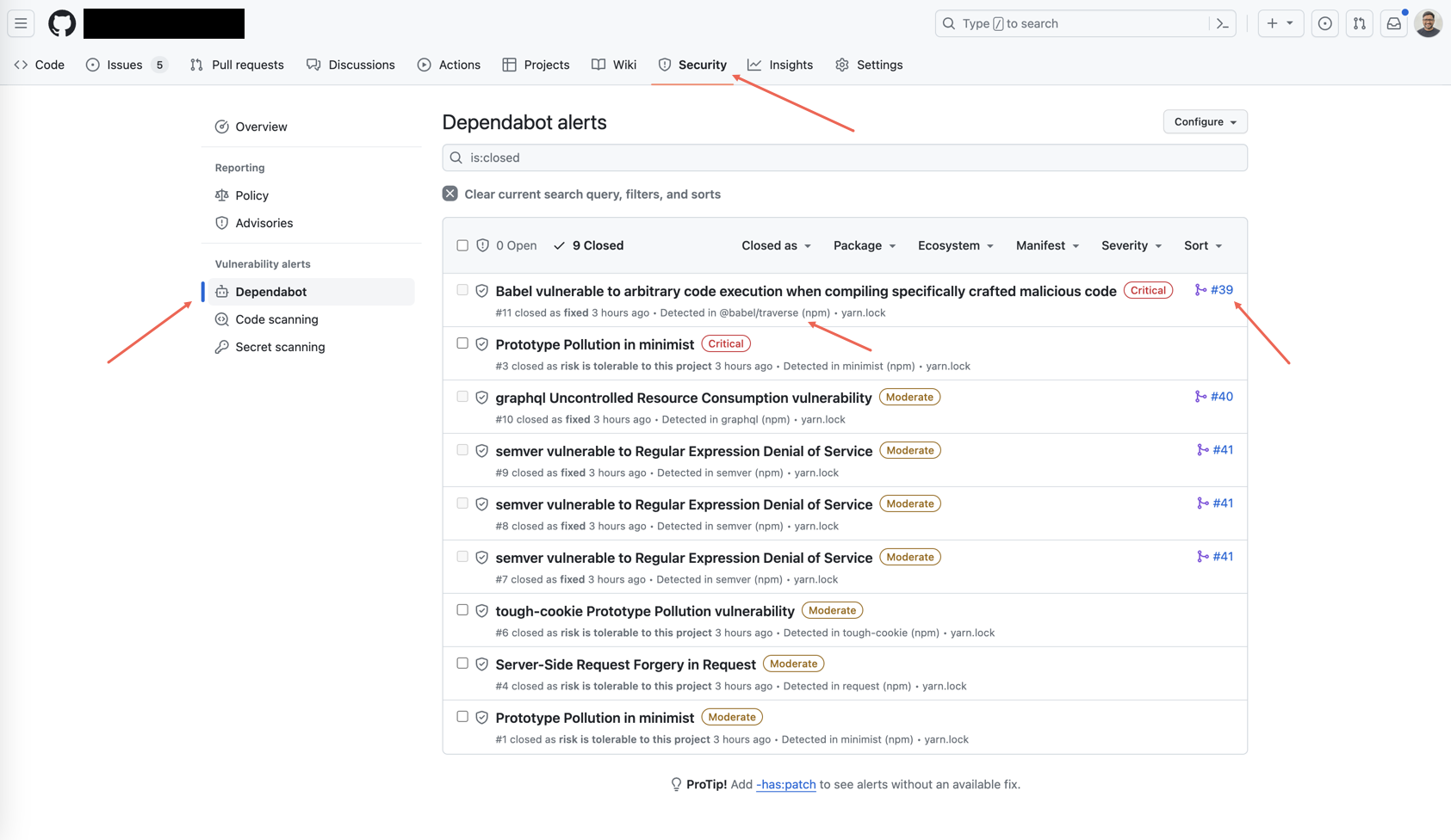
Click on the “security” tab of the GitHub project, where you can see different issues related to your project. If you enabled Dependabot, you can see different alerts raised by it, as shown in the snap below.
How does Dependabot work?
Dependabot relies heavily on semantic versioning which has the pattern of x.y.z where
- x - major version
- y - minor version
- z - patch version
In general, changes in z indicate minor code changes, bug fixes that wouldn’t change the functionality of the package. Changes in y, indicate there is some new functionality added, with backward compatibility. Changes in z, would say there are breaking changes.
Dependabot follows the below steps:
- It checks your project’s dependency files (for example: package.json, yarn.lock etc.) to identify any outdated and insecure dependencies.
- Dependabot opens a pull request with the updated dependency and suggests the version compatible.
- The pull request created by Dependabot will include relevant information, such as release notes, security vulnerabilities, bug fixes, and features.
How Dependabot fixes Node.js dependencies
For JavaScript (npm and yarn), Dependabot updates both your package.json and your yarn.lock (or package-lock.json) in the same pull request. It ensures that all your dependencies are compatible and that your lockfile is updated to match the changes in the package.json file.
Let’s take your example of a project X with a dependency tree of A -> B -> C.
Suppose there is a security vulnerability in C that affects the functionality of your project X. In this case, Dependabot will detect the vulnerability through its automated checks and create a pull request to upgrade the dependency C to a non-vulnerable version.
Now, since upgrading C may affect B, Dependabot will create another pull request to upgrade the dependency B to a version that is compatible with the updated version of C.
And since upgrading B may affect A, Dependabot will create one more pull request to upgrade the dependency A to a version compatible with the updated version of B, which, in turn, must be compatible with the updated version of C.
Finally, dependent on the version of A you are using, it is possible that there are significant changes, and so upgrading A may cause conflicts with other dependencies, files, or code. Hence, it is essential to review all the corresponding pull requests and ensure that they pass the project’s tests and requirements.
Dependabot may even choose to update all related dependencies at once to ensure complete compatibility verification. But updating every dependent package at once may be challenging, so it is crucial to review all pull requests, tests, and requirements carefully.
Conclusion
Dependabot is an excellent tool for ensuring that your project’s dependencies are up-to-date and secure. Its ability to identify and fix vulnerabilities promptly and safely has made it an indispensable tool for developers. To keep your project secure, it is essential to rely on Dependabot to detect updates and promptly test and review its modifications.